Slow Your Roll: Texas Judges Need Guidance on Ordering Direct Access in TROs

Texas judges need guidance on granting direct access to electronic devices through TROs and temporary injunctions.

Texas judges need guidance on granting direct access to electronic devices through TROs and temporary injunctions.

Does Texas law allow direct access to a departing employee’s computer or other device? Let’s apply the Texas Supreme Court’s decisions in Weekley Homes and Shipman.
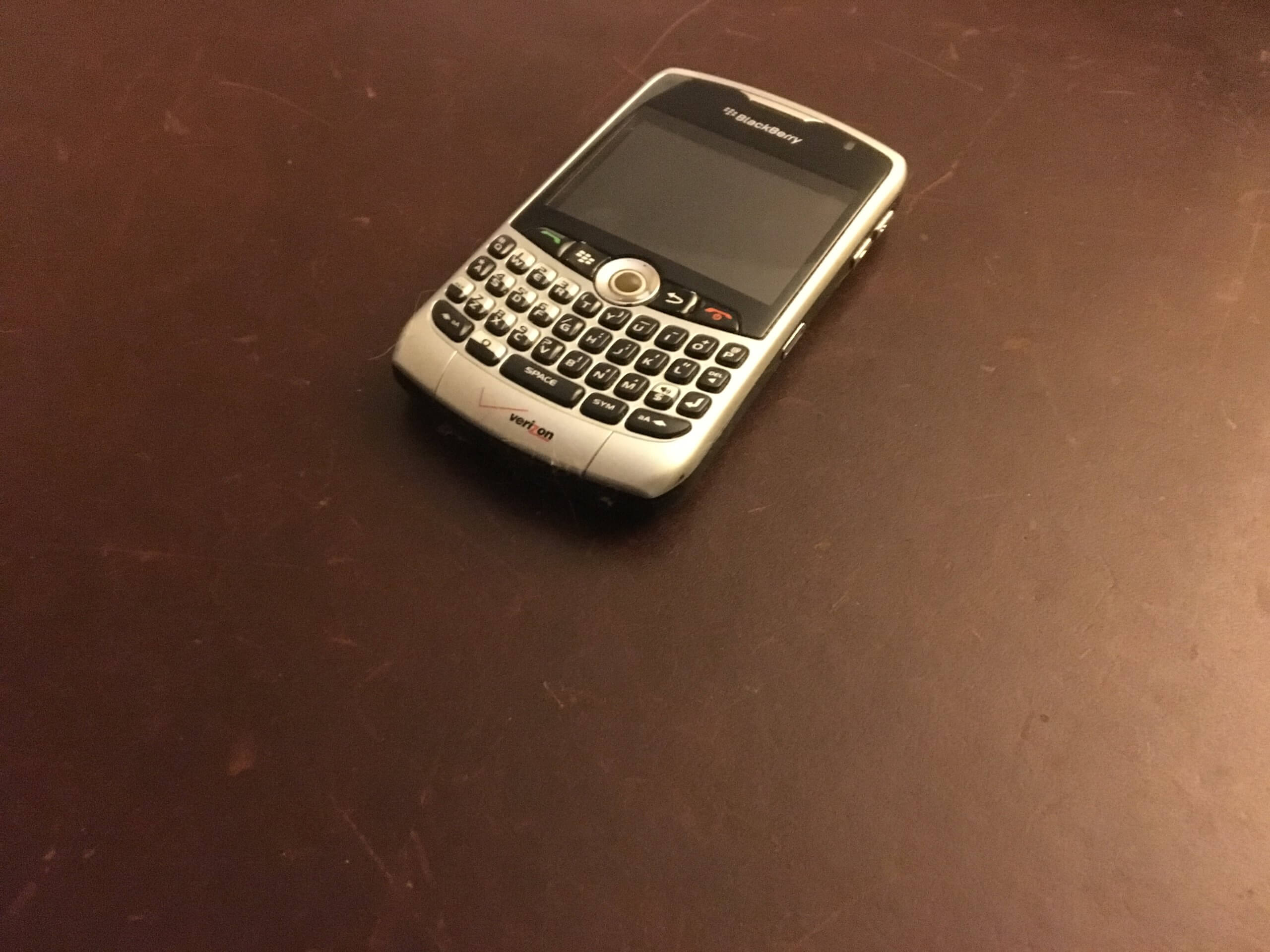
What can we learn from the emails and text messages in the Roger Stone indictment?

Find out the most important issue to address first when a key employee or executive leaves your client’s company to work for a competitor.